E12- Google paid $5B for security acquisition, apple's newest chip, something about the dark web and 3 free resources
Hello Friends,
Hope you are doing well.
Google paid $5B+ for this company to firm up their cloud security
Cloud Security is top of mind for Vendors to differentiate and get market share.
Google, the #3 cloud vendor by revenue, is buying cybersecurity company Mandiant, a threat intelligence firm for $5.4 billion. Mandiant became well known after its 2013 China espionage campaign report. Enterprises call upon mandiant in case of a cyberSecurity incident.
Can Google make its Cloud offerings attractive by having Mandiant in its corner?
What are the trade-offs of apple's mind-boggling performance chips?
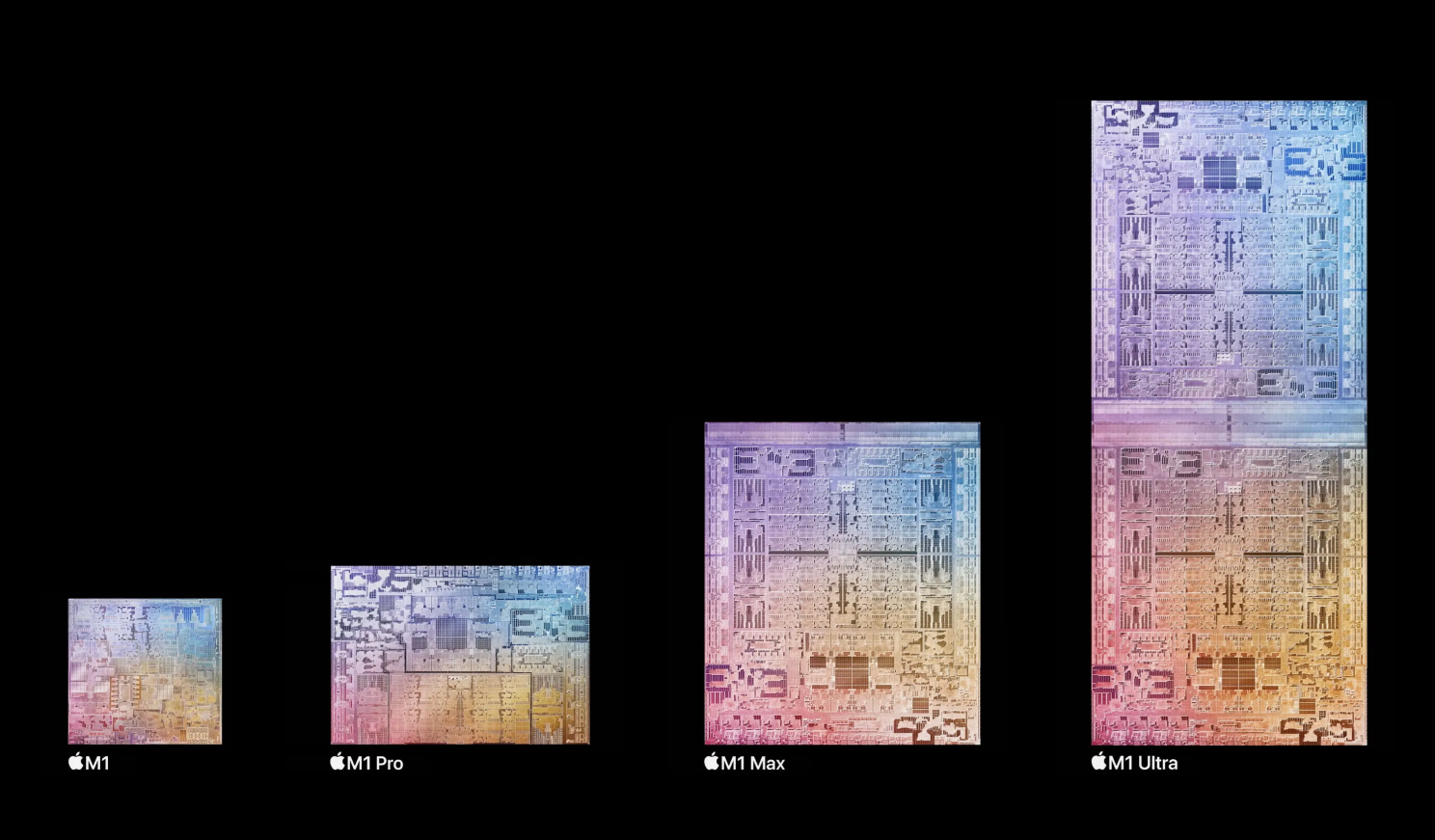
Apple's Silicon Chips investments are paying off and support their narrative of innovation.
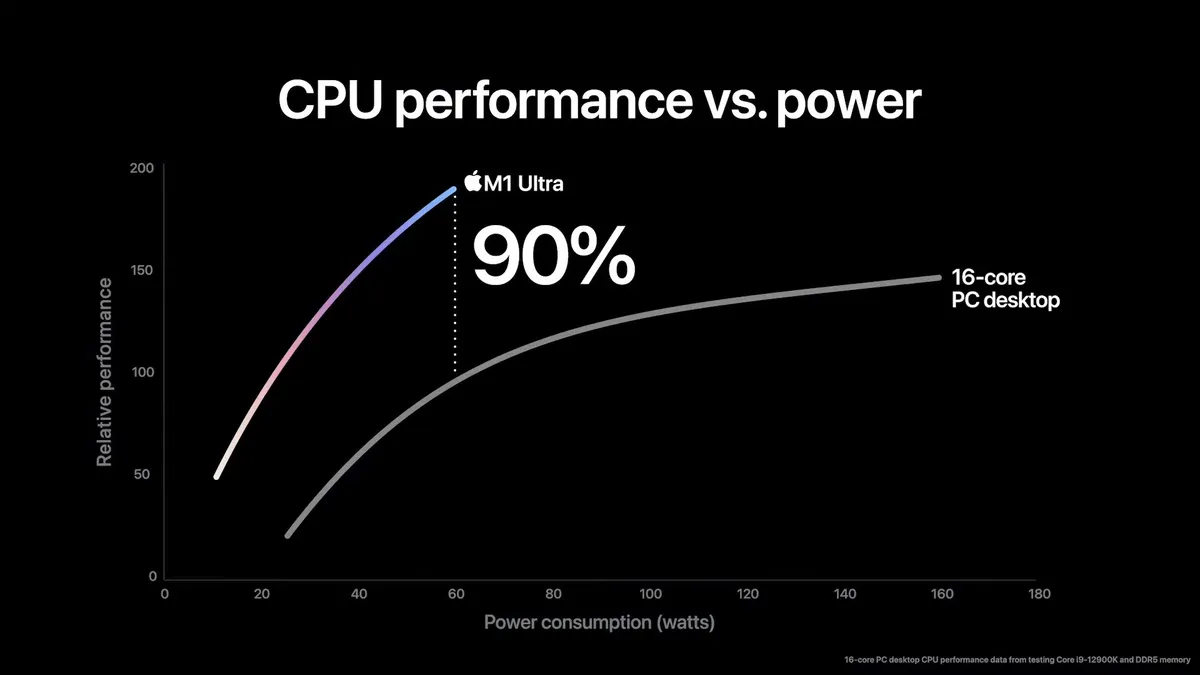
Last week, Apple launched the M1 Ultra chipset and pushed the envelope further. It is keeping Moore's Law alive & kicking. M1 Ultra will offer 128GB unified memory, 90% faster than Intel's i9012900K, uses 100W less power. 🤯 But, advancements in packaging won't solve everything.
Due to its constraints with waste heat generation and power consumption, It won't come to laptops. Its complexity in build also lends itself to high costs (Mac studio with m1 max is $1,999 but with m1 ultra is $3,999).
A great example of incremental innovation, but who is the target user base for M1 Ultra? what do you think?
I bet you didn't know about the dark web?
Cyber Criminals steal customer credit cards or personal information, sell it on the 'dark web', but do you know how and where the dark web exists?.
Websites on the dark web use onion addresses instead of domain names, called "tor addresses". These addresses are cryptographic, don't have a domain name server or IP lookup. You can only use tor browsers or ones supporting the "tor" protocol to access these addresses. Tor bounces the ".onion" traffic through three random nodes and encrypts it at every bounce.
A lot of shady stuff sells on the unregulated dark web and, it is not the most secure space for anyone who is curious.
2 Free Books downloads on building Data Applications. Free cyber Security reference architecture

Microsoft publishes a library for companies to define their target cybersecurity state architecture. These architecture templates cover on-premises, mobile devices, multi-cloud, and IT/OT Operations.
The latest ver of these templates is available here 👉 [aka.ms/MCRA]. Link in the comment.
**Architecting Data-Intensive SaaS Applications: Building Scalable Software with Snowflake 👉 [bit.ly/3I70VYr] Link in comment
The Founder’s Guide to Building Data Apps on Snowflake
It is a great book to read on building data applications and understanding snowflakes’ philosophy 👉 [bit.ly/3JbcJdM] Link in comment
What more would you like to know?